This is a div block with a Webflow interaction that will be triggered when the heading is in the view.
Modernize your cloud. Maximize business impact.
Recent data shows that while 89% of organizations provide HIPAA Privacy Rule training and 81% cover the Security Rule, only 50% actually test employees on this training at least annually. For SMBs, this gap underscores the risk: disaster recovery plans must not only ensure system uptime but also safeguard protected health information (PHI) in line with HIPAA standards.
Aligning disaster recovery strategies with HIPAA’s privacy, security, and breach notification rules empower SMBs to reduce the likelihood of compliance failures, avoid costly penalties, and maintain patient trust even in the face of outages or cyber incidents.
This article outlines how SMBs can design disaster recovery strategies that meet HIPAA requirements without adding unnecessary complexity. It covers practical steps, AWS-native tools, and expert approaches to protect PHI while ensuring business continuity.
Key takeaways:
- HIPAA-aligned DR is non-negotiable: Ensuring PHI availability, integrity, and recoverability is essential for both compliance and patient trust.
- Define clear recovery objectives: RTO and RPO must be set for critical systems like EHRs, billing, and lab apps to meet HIPAA standards.
- Automate and secure backups: AWS Backup, Amazon RDS snapshots, Amazon S3 versioning, and S3 Object Lock help prevent data loss, tampering, and accidental deletion.
- Test, monitor, and audit continuously: Regular disaster recovery drills, AWS CloudTrail logs, AWS Config, AWS Security Hub, and Amazon GuardDuty ensure operational readiness and regulatory compliance.
- Partnering with Cloudtech accelerates compliance: Cloudtech combines deep AWS expertise with healthcare SMB experience to implement robust, HIPAA-compliant disaster recovery strategies efficiently and reliably.
What happens when disaster recovery isn't aligned with HIPAA compliance?
A recovery strategy that isn’t HIPAA-compliant exposes the organization to regulatory penalties, potential breaches of sensitive data, and loss of patient trust. In other words, it’s a compliance gap with real legal and financial consequences.
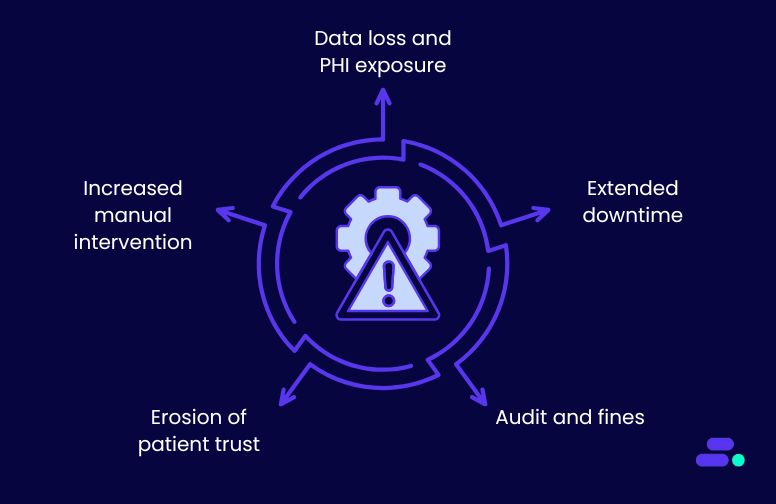
Key risks of non-aligned disaster recovery:
- Data loss and PHI exposure: Without HIPAA-compliant backups, PHI may be permanently lost or exposed in an outage, violating the privacy and security rules.
- Extended downtime: Non-compliant DR plans often lack recovery time objectives (RTOs) and recovery point objectives (RPOs) that meet HIPAA’s standard for timely access to health data.
- Audit and fines: HIPAA requires covered entities and business associates to demonstrate compliance. Gaps in disaster recovery can result in failed audits, leading to fines that range from thousands to millions of dollars.
- Erosion of patient trust: Beyond penalties, patients expect their health data to remain secure and accessible. A breach of this trust can be more damaging than financial loss.
- Increased manual intervention: Without automation and monitoring (as encouraged by AWS best practices), IT teams face delays in restoring services, creating compliance and operational risks.
In short, a disaster recovery plan that isn’t HIPAA-aligned exposes healthcare SMBs to data vulnerabilities, regulatory consequences, and reputational damage. Aligning DR with HIPAA ensures not only legal compliance but also resilience, continuity of care, and patient confidence.
Step-by-step process for performing HIPAA compliant disaster recovery

AWS is well-suited for HIPAA-aligned disaster recovery (DR) because it provides secure, compliant infrastructure with built-in resilience. Features like multi-AZ replication, automated backups, and encrypted storage ensure protected health information (PHI) is both highly available and safeguarded.
On top of this, AWS offers tools to make DR both fast and auditable. AWS Elastic Disaster Recovery (DRS) enables quick failover across Regions, while AWS CloudTrail and AWS Config deliver the logs needed for HIPAA reporting. These tools enable SMBs to design DR strategies that not only minimize downtime but also maintain HIPAA’s required safeguards for confidentiality, integrity, and availability of PHI.
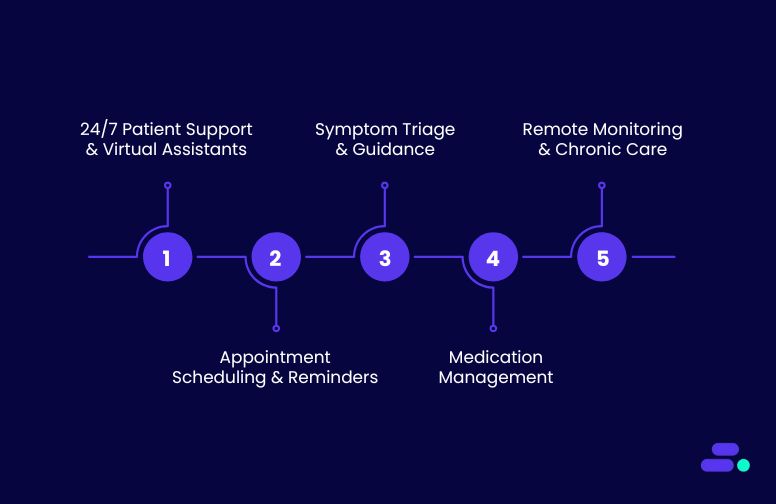
SMBs can follow a step-by-step process to perform HIPAA compliant disaster recovery:
1. Identify PHI and compliance scope
Before building disaster recovery, SMBs need a clear understanding of where protected health information (PHI) resides and how it flows across their systems. This ensures every workload that stores or processes PHI is covered under HIPAA safeguards, minimizing compliance gaps and protecting patient trust.
How to do this with AWS:
- Use AWS Macie to automatically scan and classify PHI within S3 buckets.
- Leverage AWS Config to track PHI-related workloads and validate that they meet HIPAA-required configurations.
- Centralize resource visibility with AWS Organizations to map which accounts and workloads fall under HIPAA compliance obligations.
Use case: A regional healthcare SMB uploads patient records and lab results into Amazon S3. They use AWS Macie to detect PHI such as social security numbers and health IDs, then apply AWS Config rules to verify encryption at rest and in transit.
Through AWS Organizations, they centralize compliance policies across multiple accounts, ensuring PHI workloads are scoped properly before defining their disaster recovery plan.
2. Define recovery objectives
HIPAA requires healthcare organizations to ensure PHI remains available and intact during a disaster. To achieve this, SMBs must define recovery time objectives (RTO), like how quickly systems must be restored, and recovery point objectives (RPO), like how much data can be lost without violating compliance.
By aligning these objectives with business-critical systems such as electronic health records (EHRs), billing platforms, and lab applications, SMBs can prioritize recovery where it matters most.
How to do this with AWS:
- Use AWS Elastic Disaster Recovery (AWS DRS) to set RPO/RTO targets and replicate workloads with minimal data loss.
- Leverage Amazon CloudWatch metrics to monitor workload performance against defined RTO thresholds.
- Run compliance-driven simulations with AWS Fault Injection Simulator (FIS) to validate if recovery objectives meet HIPAA availability standards.
Use case: A mid-sized healthcare SMB running an EHR system on Amazon RDS defines an RPO of 15 minutes and an RTO of 1 hour. They use AWS DRS to continuously replicate the EHR database across Availability Zones, configure CloudWatch alarms to track recovery SLAs, and regularly test scenarios with AWS FIS.
This ensures that, even during outages, PHI remains both available and compliant with HIPAA’s integrity and availability requirements.
3. Design a HIPAA-ready architecture
To meet HIPAA’s requirements for confidentiality, integrity, and availability of PHI, SMBs need to design their disaster recovery architecture with both resilience and security in mind.
This means workloads must withstand outages across Availability Zones (AZs) or even Regions, while ensuring PHI is encrypted, access-controlled, and isolated from unauthorized traffic. A HIPAA-ready architecture balances technical robustness with strict compliance safeguards.
How to do this with AWS:
- Enable multi-AZ and multi-Region deployments with services like Amazon RDS, Amazon S3 Cross-Region Replication, and AWS Elastic Disaster Recovery for fault tolerance.
- Encrypt PHI at rest and in transit using AWS Key Management Service (KMS) and enforcing TLS across all communication channels.
- Apply least-privilege IAM policies and network segmentation with AWS Identity and Access Management (IAM), Amazon VPC, and security groups to restrict access to PHI workloads.
Use case: A regional healthcare SMB runs its billing and patient management system on Amazon RDS and Amazon EC2. To ensure HIPAA alignment, they configure multi-AZ failover for their RDS database, use S3 cross-region replication to back up billing records, and encrypt all PHI with KMS-managed keys.
Their security team enforces IAM role-based access and VPC segmentation so only authorized clinicians and billing staff can reach the sensitive workloads. This design ensures resilience against outages while maintaining HIPAA-grade data security.
4. Automate backups and replication
A HIPAA-aligned DR plan requires that PHI is continuously protected without relying on manual processes. Automated backups and replication not only reduce human error but also ensure that data can be quickly restored in case of outages, corruption, or accidental deletion. By combining immutability and versioning, SMBs create an auditable, compliant trail of PHI data protection.
How to do this with AWS:
- Enable AWS Backup to centralize and automate backups across services like Amazon RDS, Amazon EFS, and DynamoDB.
- Use Amazon RDS automated snapshots and point-in-time recovery to protect EHR or billing databases.
- Configure Amazon S3 versioning and Object Lock to prevent tampering or accidental deletions of PHI backups.
Use case: A growing healthcare SMB runs its electronic lab results system on Amazon RDS and stores patient reports in Amazon S3. They configure AWS Backup to automatically capture daily RDS snapshots and enforce Object Lock on S3 buckets holding PHI.
If a staff member accidentally deletes or modifies a report, the SMB can restore it from an immutable backup, ensuring compliance with HIPAA’s data integrity and availability requirements.
5. Implement disaster recovery orchestration
A HIPAA-compliant DR plan cannot stop at backups, it must also ensure rapid workload recovery in the event of an outage. Orchestration brings automation and repeatability, reducing recovery times and minimizing human error during stressful failover scenarios. By continuously testing and validating DR runbooks, SMBs align with HIPAA’s requirement to maintain PHI availability.
How to do this with AWS:
- Use AWS Elastic Disaster Recovery (DRS) to replicate workloads from primary to standby environments with minimal downtime.
- Configure automated failover workflows using AWS CloudEndure or Step Functions to orchestrate multi-tier application recovery.
- Regularly test recovery plans through controlled failover drills to validate compliance with HIPAA’s availability standards.
Use case: A healthcare SMB hosting its billing and claims system on Amazon EC2 replicates workloads to a secondary Region using AWS DRS. They set up automated failover playbooks with AWS Step Functions to bring critical services online within their defined RTO. Twice a year, the IT team runs simulated failover tests to confirm systems can recover quickly while meeting HIPAA’s operational availability rules.
6. Monitor and audit continuously
HIPAA compliance isn’t a one-time setup. It requires ongoing monitoring and evidence that security and availability controls are enforced at all times. Continuous visibility helps SMBs detect unauthorized access, configuration drift, or security threats before they impact PHI. Auditability also ensures organizations can demonstrate compliance during regulatory reviews.
How to do this with AWS:
- Enable AWS CloudTrail and AWS Config to track all API activity and resource changes across accounts.
- Use AWS Security Hub and GuardDuty to continuously monitor for misconfigurations, anomalies, or suspicious activities tied to PHI workloads.
- Set up log retention policies in Amazon S3 and Glacier to meet HIPAA’s requirement for forensic investigations and long-term compliance audits.
Use case: A healthcare SMB runs its patient scheduling system on Amazon RDS and EC2. With AWS CloudTrail enabled, every API call is logged, while AWS Config flags non-compliant security group changes. GuardDuty alerts the IT team about unusual login attempts, and all logs are securely stored in Amazon S3 with Object Lock, ensuring immutability for HIPAA audit readiness.
7. Test and validate regularly
A disaster recovery plan is only effective if it works when needed. HIPAA explicitly requires organizations to test and train their workforce on contingency procedures. Regular DR drills not only validate the technical failover process but also prepare teams to respond quickly during real incidents. Documenting results is essential for proving compliance in HIPAA audits.
How to do this with AWS:
- Use AWS Elastic Disaster Recovery (DRS) or CloudEndure to run non-disruptive failover tests without impacting production workloads.
- Leverage AWS Fault Injection Simulator to perform chaos engineering experiments and validate resilience against failures.
- Automate reporting with AWS Systems Manager to capture test outcomes and retain evidence for compliance audits.
Use case: A mid-sized dental practice runs its billing application on Amazon RDS and EC2. Twice a year, the IT team uses AWS DRS to spin up a recovery environment in another Region and measure failover time against the defined RTO. They document the results in AWS Systems Manager runbooks, creating a compliance trail that auditors can review to confirm HIPAA readiness.
8. Update policies and procedures
Disaster recovery is also about people and processes. HIPAA requires that contingency plans be backed by documented policies and workforce training. Updating policies ensures that technical safeguards (like backups, failover, and monitoring) align with organizational procedures for incident response.
Training staff makes sure employees know their roles during an outage, helping maintain the availability, confidentiality, and integrity of PHI.
How to do this with AWS:
- Integrate AWS backup and DR workflows into internal SOPs so staff know when and how to trigger failover or recovery.
- Use AWS Identity and Access Management (IAM) to enforce role-based access policies that map directly to DR responsibilities.
- Leverage AWS Artifact to access HIPAA-related compliance reports and share them with staff during training and audits.
Use case: A regional urgent care provider documents new policies for how its staff should respond if its Electronic Health Record (EHR) system becomes unavailable. The IT team integrates AWS Backup and AWS DRS workflows into the policy playbook and uses IAM roles to define which staff members can initiate recovery.
During quarterly training, employees review these procedures alongside HIPAA guidelines, ensuring both compliance and operational readiness.

Pro tip: Working with an AWS Partner like Cloudtech is highly advisable for HIPAA-relevant disaster recovery because certified partners bring deep expertise in AWS security, compliance, and healthcare workloads.
They understand how to map HIPAA safeguards to AWS services, design resilient multi-Region architectures, and implement proper encryption, monitoring, and audit controls.
See how other SMBs have modernized, scaled, and thrived with Cloudtech’s support →
How does Cloudtech help healthcare SMBs set up HIPAA-compliant disaster recovery?
What sets Cloudtech apart is its deep AWS expertise combined with a human-centric approach tailored for SMBs. Cloudtech focuses exclusively on helping smaller organizations modernize with AWS while staying compliant with complex frameworks like HIPAA.
For healthcare SMBs, this means DR strategies that not only meet technical requirements but also align with regulatory safeguards for PHI protection and availability.
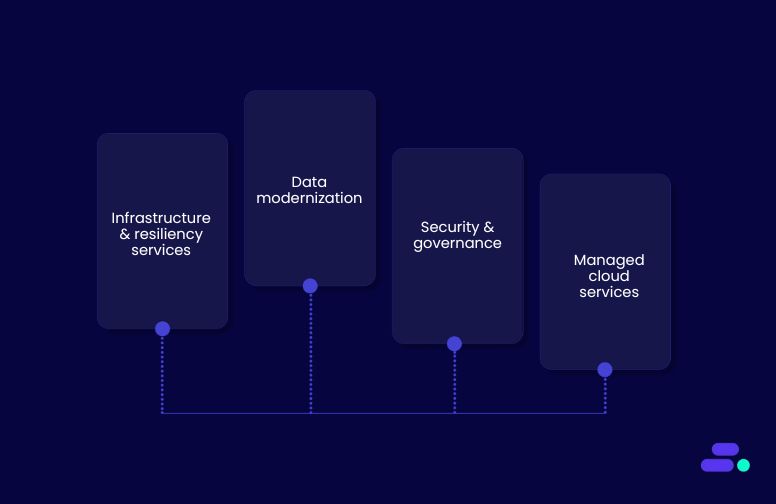
Relevant Cloudtech services for HIPAA-compliant DR:
- Infrastructure & resiliency services: Multi-AZ and multi-Region design, backup automation, and failover orchestration using AWS Elastic Disaster Recovery.
- Data modernization: Secure storage, encryption, and compliant data lake/warehouse strategies for PHI.
- Security & governance: HIPAA-aligned identity management, monitoring with CloudTrail, GuardDuty, and AWS Config, plus audit-ready logging.
- Managed cloud services: Ongoing monitoring, DR drills, and policy alignment to keep systems and staff compliant over time.
By combining these services, Cloudtech ensures healthcare SMBs achieve HIPAA-compliant DR that is resilient, cost-efficient, and continuously audit-ready.
Wrapping up
HIPAA-compliant disaster recovery is a critical safeguard for protecting patient data, maintaining trust, and ensuring uninterrupted operations. For healthcare SMBs, even minor misconfigurations or gaps can have serious regulatory, financial, and reputational consequences.
Partnering with an AWS expert like Cloudtech ensures DR strategies are designed and implemented with precision. With their support, healthcare teams can focus on patient care and growth, confident that critical workloads remain protected and compliant.
Connect with Cloudtech today to build a HIPAA-compliant disaster recovery strategy that safeguards PHI and keeps your operations running smoothly.
FAQs
1. Why is disaster recovery critical for HIPAA compliance in SMBs?
Disaster recovery ensures that Protected Health Information (PHI) remains available, intact, and recoverable during outages, cyberattacks, or human errors. HIPAA mandates that healthcare organizations implement technical safeguards to maintain data availability and integrity, making DR an essential compliance component.
2. Can small healthcare SMBs implement HIPAA-compliant DR without AWS expertise?
While technically possible, doing so is highly challenging. Configuring multi-AZ/Region replication, secure backups, failover orchestration, and audit logging requires deep AWS knowledge. Without it, gaps in compliance or misconfigured systems could expose PHI to risks.
3. How often should SMBs test their HIPAA-compliant DR plans?
HIPAA recommends testing and workforce training at least annually. Frequent testing—quarterly or semi-annual—helps validate that backups, failovers, and alerting mechanisms work correctly, while also familiarizing staff with DR processes to reduce human errors during incidents.
4. What AWS services are most useful for HIPAA-aligned disaster recovery?
AWS offers several critical tools for DR, including AWS Backup, RDS snapshots, Amazon S3 with Object Lock, AWS Elastic Disaster Recovery (DRS), CloudEndure, CloudTrail, AWS Config, Security Hub, and GuardDuty. These services help SMBs automate backups, orchestrate failovers, and maintain audit-ready logs.
5. How does Cloudtech add value beyond standard AWS DR capabilities?
Cloudtech tailors disaster recovery strategies for healthcare SMBs by aligning AWS services with HIPAA requirements. They implement automated backups, replication, and failover, validate recovery objectives, enforce least-privilege access, and provide continuous monitoring and staff training, ensuring DR is compliant, resilient, and fully operational.

Get started on your cloud modernization journey today!
Let Cloudtech build a modern AWS infrastructure that’s right for your business.