This is a div block with a Webflow interaction that will be triggered when the heading is in the view.
Modernize your cloud. Maximize business impact.
Many businesses implementing cloud assume that the security of their hosted data and applications rests with the service provider. They forget that cloud security is a shared responsibility. Without actively implementing cloud security best practices, gaps widen, leaving critical data and applications vulnerable despite the inbuilt security controls.
For SMBs implementing AWS Cloud, the real power comes from combining its built-in protections with cloud security best practices. SMBs that embrace this shared responsibility model don’t just survive, they thrive.
This article breaks down 9 AWS cloud security best practices SMBs should implement to protect workloads, strengthen compliance, and build a resilient cloud environment.
Key takeaways:
- Cloud security requires best practices, not shortcuts: SMBs must go beyond reactive defenses with layered, automated, and scalable controls.
- Shared responsibility is key: AWS secures the cloud infrastructure, but SMBs must protect workloads, identities, and data.
- Automation reduces risk and cost: Automating compliance, monitoring, and response ensures consistent security without added overhead.
- Enterprise-grade security is within reach: With AWS-native tools, SMBs can achieve advanced protection without enterprise-level budgets.
- Cloudtech makes it airtight: As an AWS Advanced Tier Partner, Cloudtech tailors and enforces best-practice security frameworks that scale with SMB growth.
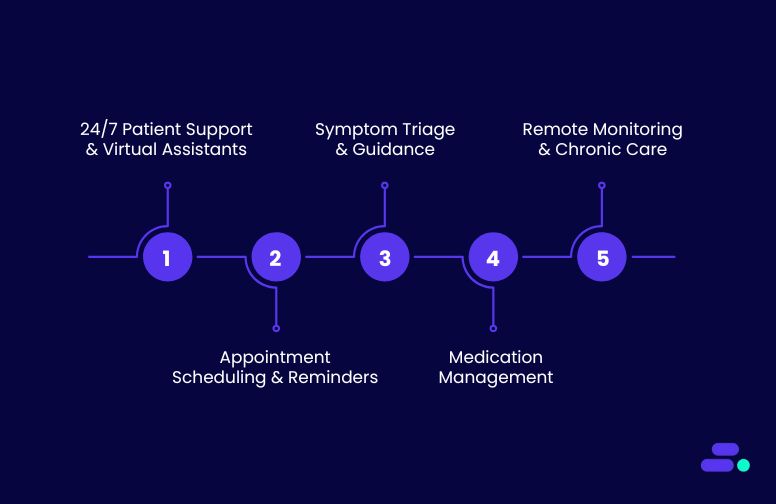
What happens if SMBs don’t follow cloud security best practices?
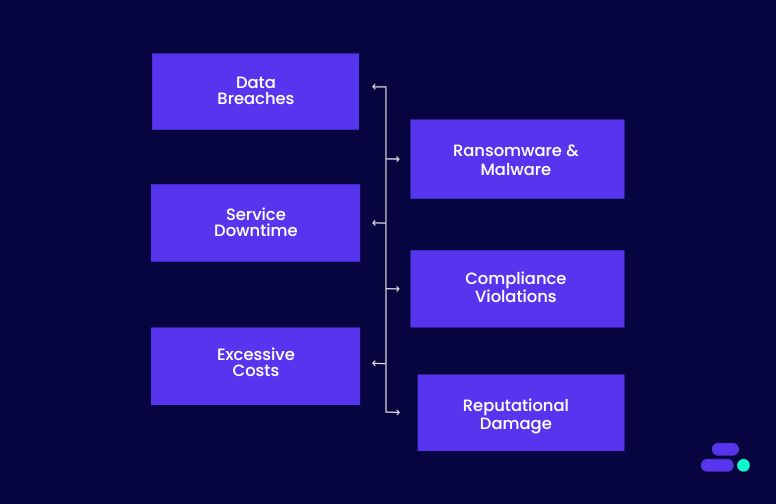
Ignoring cloud security best practices can expose SMBs to a range of operational, financial, and reputational risks. Unlike large enterprises with dedicated security teams, SMBs often lack the resources to detect and respond to threats quickly.
Without proactive measures, even workloads running on secure cloud infrastructure can become vulnerable to attacks, misconfigurations, and compliance failures.
Key risks and consequences include:
- Data breaches and exfiltration: Poorly configured access controls, unsecured Amazon S3 buckets, or mismanaged IAM roles can allow attackers to steal sensitive customer, financial, or intellectual property data. Breaches can result in regulatory fines, legal liabilities, and loss of customer trust.
- Ransomware and malware attacks: Weak network segmentation, missing patch management, and lack of runtime monitoring increase the likelihood of ransomware infection or malware propagation across cloud resources, potentially locking critical workloads.
- Service disruptions and downtime: Failure to implement redundancy, automated backups, or disaster recovery can turn hardware failures, application misconfigurations, or cyberattacks into extended downtime, impacting revenue and operations.
- Compliance violations: SMBs in regulated industries like healthcare, finance, or e-commerce risk fines and penalties if logging, auditing, and encryption standards aren’t followed. Mismanaged data residency or retention policies can trigger non-compliance.
- Excessive costs and inefficiencies: Insecure or poorly optimized cloud deployments can result in runaway resource usage, repeated recovery efforts, and inefficiencies in monitoring and incident response, driving up operational expenses.
- Reputational damage: Customers and partners expect secure handling of data. A single breach or repeated security incidents can erode trust, making it harder to acquire new clients and retain existing ones.
Failing to adopt cloud security best practices multiplies risk across infrastructure, applications, and business operations. Security must be proactive, automated, and continuous, integrating identity management, network protection, monitoring, and compliance to ensure workloads remain resilient and secure in the cloud.
9 cloud security best practices SMBs should follow to secure their data and applications

For SMBs, adopting AWS cloud security best practices means creating a resilient, scalable framework that protects data, applications, and business operations across every layer of the cloud environment.
AWS provides a rich ecosystem of services that make these best practices achievable even for lean IT teams. Continuous monitoring, threat detection, and compliance are built into the AWS platform. AWS tools like GuardDuty, Security Hub, Inspector, and Config allow SMBs to detect anomalies, enforce policies, and maintain regulatory alignment without needing large security teams.
Integrating security early in development pipelines (“shift-left” practices) with CodePipeline and automated vulnerability scans ensures that workloads are safe before deployment. Lifecycle management, logging, and cost monitoring tools like Amazon CloudWatch and Cost Explorer help SMBs optimize operations while maintaining security.
Following these 9 best practices help SMBs to implement automated, resilient, and cost-efficient security that evolves alongside their business:
1. Strong identity and access management
Effective identity and access management (IAM) is the cornerstone of cloud-native security. For SMBs, properly managing who can access what resources ensures sensitive data, applications, and workloads remain protected, even as teams grow or workloads scale. Strong IAM practices minimize risk, support compliance, and enable secure collaboration across the organization.
How to implement using AWS:
- Define roles and permission sets in AWS IAM and IAM Identity Center, assigning access based on job functions or workloads.
- Enable multi-factor authentication (MFA) for all human users and utilize temporary credentials for applications or automation tasks.
- Regularly audit and review permissions to detect and correct privilege creep.
- Integrate logging and monitoring via AWS CloudTrail to track all access and changes.
- Use Service Control Policies (SCPs) within AWS Organizations to enforce consistent access policies across multiple accounts.
Why it matters: Strong IAM reduces the attack surface by ensuring users and applications only have the permissions they need. It helps SMBs meet regulatory requirements such as HIPAA, GDPR, and PCI DSS, and prevents operational errors caused by misconfigurations or unauthorized access. With proper IAM, even lean IT teams can maintain a secure, auditable, and resilient cloud environment.
2. Network segmentation and protection
A secure network foundation is critical for safeguarding SMB applications and data in the cloud. Poorly designed networks can expose sensitive workloads to unnecessary risk. By segmenting networks, restricting traffic, and layering defenses, SMBs can limit the blast radius of an attack and ensure each part of their infrastructure is only accessible where necessary.
How to implement using AWS:
- Create Amazon VPCs with isolated public and private subnets to separate internet-facing services from internal workloads.
- Apply Security Groups for instance-level controls and Network ACLs (NACLs) for subnet-level filtering.
- Protect web-facing applications using AWS WAF for application-layer threats and AWS Shield for DDoS mitigation.
- Use VPC Endpoints to connect securely to AWS services without traversing the public internet.
- Implement AWS Transit Gateway for centralized and secure multi-VPC or hybrid network connectivity.
- Monitor network traffic using VPC Flow Logs and integrate with Amazon GuardDuty for anomaly detection.
Why it matters: Network segmentation reduces the attack surface by ensuring workloads are only exposed where necessary. It prevents lateral movement in case of compromise and safeguards customer-facing applications against web exploits and denial-of-service attacks.
For SMBs, a strong network architecture provides enterprise-grade protection while keeping costs predictable and management simple.
3. Encryption for data in transit and at rest
Data is the most valuable asset for any SMB, and protecting it is non-negotiable. Whether at rest in storage or moving between applications, unencrypted data is an easy target for attackers. Robust encryption ensures that even if systems are breached or files intercepted, the data remains unreadable and protected.
How to implement using AWS:
- Use AWS Key Management Service (KMS) to enable encryption across Amazon S3, EBS, RDS, DynamoDB, and other storage services.
- For higher security, configure Customer-Managed Keys (CMKs) with rotation policies for sensitive workloads.
- Enforce TLS (SSL) for all data transfers between applications, databases, and APIs.
- Encrypt backups and logs automatically using AWS services like AWS Backup and CloudTrail with KMS.
- Use AWS Certificate Manager (ACM) to manage SSL/TLS certificates without the operational overhead.
- Monitor key usage and access through AWS CloudTrail and set up alerts for unusual activity.
Why it matters: Encryption ensures that sensitive customer data, financial records, and intellectual property remain secure even if infrastructure is compromised. For SMBs, it’s a cost-effective way to meet compliance requirements (HIPAA, PCI DSS, GDPR) while maintaining customer trust. Strong encryption practices reduce the risk of data leaks, safeguard against insider threats, and demonstrate a proactive commitment to security.
4. Automated security monitoring and threat detection
Cyber threats are constantly evolving, and manual monitoring can’t keep up. SMBs need real-time visibility into suspicious activity to respond before small issues escalate into major breaches. Automated security monitoring enables lean IT teams to detect anomalies, privilege escalations, and unauthorized access without heavy operational overhead.
How to implement using AWS:
- Enable Amazon GuardDuty to detect anomalous behavior such as unusual API calls, unauthorized access attempts, or data exfiltration.
- Use AWS Security Hub to centralize findings across multiple AWS accounts and services, providing a single view of compliance and threats.
- Integrate Amazon Detective to investigate suspicious activity with visualized relationships between users, resources, and IP addresses.
- Automate response workflows with AWS Lambda or AWS Systems Manager to contain threats quickly.
- Feed logs from AWS CloudTrail, VPC Flow Logs, and CloudWatch into monitoring tools for comprehensive coverage.
Why it matters: For SMBs with limited security staff, automation levels the playing field against sophisticated attackers. Instead of relying on reactive, manual reviews, AWS-native monitoring tools provide continuous coverage and actionable insights. This reduces the time to detect and respond, minimizes potential damage, and ensures that businesses can stay compliant and resilient without building a large security operations center.
5. Shift-left security in development pipelines
Modern SMBs increasingly rely on rapid software releases to stay competitive. But with speed comes the risk of pushing vulnerable code into production. Shift-left security embeds checks early in the development lifecycle within CI/CD pipelines, so vulnerabilities are caught before workloads are deployed.
This proactive approach reduces the cost and impact of fixing issues later while improving overall application security.
How to implement using AWS:
- Use AWS CodePipeline to automate build, test, and deployment stages while embedding security checks.
- Integrate Amazon Inspector to scan for vulnerabilities in EC2 instances, containers, and Lambda functions.
- Add container image scanning through Amazon ECR (Elastic Container Registry) to detect known vulnerabilities before pushing images to production.
- Apply policy-as-code with AWS Config and AWS IAM Access Analyzer to enforce compliance and prevent misconfigurations.
- Automate testing with third-party integrations (e.g., Snyk, Checkmarx) directly within CodeBuild or CodePipeline for comprehensive coverage.
Why it matters: For SMBs, catching security issues in production can lead to costly downtime, reputational damage, and compliance failures. By shifting security left, businesses create a culture of “secure by design” while accelerating safe releases. This ensures developers focus on innovation without sacrificing resilience, helping SMBs build customer trust and reduce long-term security costs.
6. Compliance and governance by design
Meeting compliance requirements isn’t just about passing audits. It's about embedding trust into every layer of the cloud environment. For SMBs in regulated industries, failing to address compliance can quickly lead to fines, legal risk, and lost credibility. Governance by design ensures that compliance is continuously enforced through automation, not as an afterthought or one-time checklist.
How to implement using AWS:
- Use AWS Config to continuously monitor configurations against compliance rules and automatically remediate violations.
- Leverage AWS Control Tower to establish a secure, multi-account landing zone with guardrails aligned to compliance frameworks.
- Automate evidence collection and reporting with AWS Audit Manager, simplifying audits for standards like HIPAA, GDPR, and PCI DSS.
- Enable AWS CloudTrail and AWS Security Hub for centralized logging, monitoring, and compliance visibility.
- Integrate compliance findings with dashboards and alerts to ensure real-time visibility for stakeholders.
Why it matters: For SMBs, manual compliance processes are often slow, error-prone, and expensive. Automating governance not only reduces human error but also strengthens trust with customers, partners, and regulators. By making compliance part of the cloud architecture itself, SMBs can scale with confidence, avoid regulatory pitfalls, and focus on growth without being slowed down by audit fatigue.
7. Backup and disaster recovery planning
Outages, ransomware, and accidental deletions can strike without warning. For SMBs with limited IT resources, a single disruption can lead to significant downtime, lost revenue, and damaged trust.
A well-designed backup and disaster recovery (DR) plan ensures business continuity, giving businesses the confidence that their data and applications can survive unexpected events.
How to implement using AWS:
- Use AWS Backup to centrally manage, automate, and monitor backups across AWS services and on-premises workloads.
- Design workloads with multi-AZ replication and consider cross-region backups for stronger disaster recovery.
- Define Recovery Point Objectives (RPOs) and Recovery Time Objectives (RTOs) based on application criticality.
- Regularly test restores using AWS Elastic Disaster Recovery (DRS) to validate recovery readiness.
- Apply lifecycle policies to optimize storage costs while maintaining compliance requirements.
Why it matters: Without a tested backup and DR strategy, downtime can escalate from hours to days, eroding customer confidence and creating financial setbacks. By planning ahead with AWS-native tools, SMBs can recover quickly, minimize disruption, and ensure their business stays resilient no matter what happens.
8. Continuous optimization and cost-aware security
Security and cost optimization often go hand in hand. SMBs need to ensure that security controls are always enforced without overspending on unused or misconfigured resources. By continuously reviewing usage patterns and aligning them with security best practices, businesses can protect their environment while staying within budget.
How to implement using AWS:
- Use AWS Cost Explorer to track spending and correlate costs with specific projects through resource tagging.
- Set up Amazon CloudWatch alarms for unusual spikes in activity that may signal security incidents or misconfigurations.
- Apply AWS Budgets and Trusted Advisor recommendations to identify unused or underutilized resources.
- Regularly audit S3 lifecycle rules, permissions, and logging to prevent unnecessary exposure and storage costs.
- Automate cleanup of unused keys, roles, and security groups to reduce the attack surface and optimize costs.
Why it matters: SMBs often operate under tight budgets, making it critical to balance robust security with cost efficiency. Continuous optimization ensures that resources remain secure, lean, and right-sized, preventing both wasted spend and security blind spots. This approach helps SMBs stay secure without sacrificing financial agility.
9. Security awareness and culture building
Even the most advanced AWS security tools can’t protect an organization if employees unknowingly open the door to threats. Phishing, weak passwords, and accidental data exposure are among the most common causes of breaches for SMBs. Building a strong security culture ensures that people, and not just technology, play an active role in protecting cloud workloads.
How to implement using AWS:
- Use AWS IAM Access Analyzer to detect unintended public or cross-account access to resources and educate teams on resolving issues.
- Enforce MFA across all user accounts using IAM Identity Center, reinforcing the habit of secure logins.
- Enable AWS CloudTrail & GuardDuty alerts and share findings with staff during regular security training sessions.
- Provide least-privilege access tied to roles, ensuring employees only interact with the resources they actually need.
Why it matters: Technology is only half of the equation. Human behavior often decides whether a breach happens or not. By instilling security awareness and good practices in daily operations, SMBs drastically reduce risks from accidental misconfigurations, phishing attempts, or insider mistakes. A culture-first approach makes every employee a security partner, not just a bystander.
Implementing these practices helps SMBs move beyond basic cloud protections to a proactive, automated, and resilient security posture, safeguarding data, applications, and business operations in the AWS cloud.

Why risk gaps in security? For SMBs, even small missteps can expose critical data. That’s where AWS experts like Cloudtech can ensure best practices are implemented correctly, compliance is automated, and cloud security scales seamlessly with the business.
How does Cloudtech help SMBs strengthen their cloud security?
Most AWS partners focus on security compliance checklists. Cloudtech goes further, designing SMB-first security architectures that balance cost, usability, and resilience. Its team of former AWS professionals combines deep technical expertise with real-world SMB challenges, ensuring security isn’t just implemented, but continuously optimized to evolve with the business.
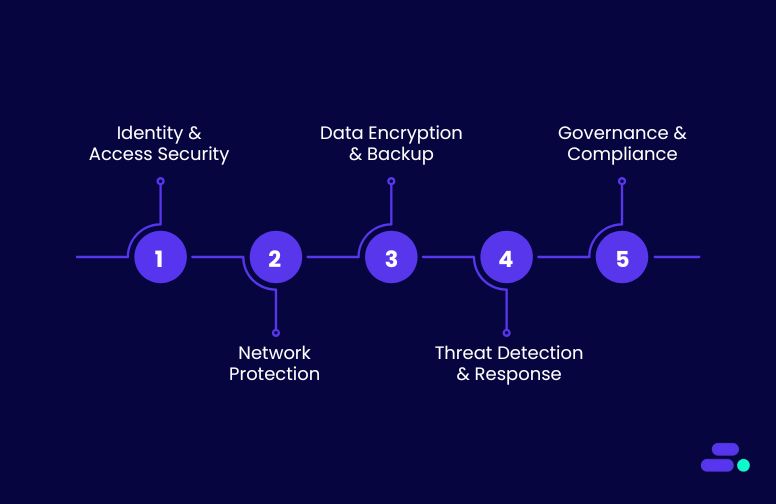
Key Cloudtech services for strengthening cloud security:
- Identity and access security: Cloudtech sets up centralized identity with AWS IAM and IAM Identity Center, enforces MFA, manages privileged accounts, and applies least-privilege policies to safeguard user and service access.
- Network segmentation and protection: Using Amazon VPC, security groups, network ACLs, AWS WAF, and AWS Shield, Cloudtech isolates workloads, blocks malicious traffic, and reduces exposure to external threats.
- Data encryption and backup security: Cloudtech secures sensitive data with AWS KMS, encrypts backups and logs, and enables automated replication across multiple Availability Zones for data integrity and resilience.
- Threat detection and incident response: With Amazon GuardDuty, CloudWatch, and AWS Security Hub, Cloudtech provides continuous threat detection, centralized alerting, and automated remediation to quickly contain risks.
- Governance, compliance, and auditing: Leveraging AWS Config, Control Tower, and Audit Manager, Cloudtech enforces policies, monitors compliance in real time, and produces audit-ready reports for regulations like HIPAA, GDPR, and PCI DSS.
Through these capabilities, SMBs don’t just “check the security box,” they gain an AWS-architected, SMB-tailored security model. Cloudtech ensures controls are not only compliant but also cost-aware, automated, and practical for lean IT teams, giving SMBs the confidence to stay secure while scaling.
See how other SMBs have modernized, scaled, and thrived with Cloudtech’s support →
Wrapping up
Security done halfway is a hidden risk, where misconfigured controls, unmonitored activity, or weak compliance can expose critical data and stall growth. Adopting AWS best practices isn’t optional anymore. It’s the foundation for resilient, scalable operations in a threat-heavy digital landscape.
With the help of an AWS expert like Cloudtech, SMBs can implement these best practices with precision, building airtight security frameworks, enforcing least-privilege access, automating compliance, and continuously monitoring workloads. The result is a proactive, cost-aware security posture that lets leaders focus on growth while knowing their cloud is secured against evolving threats.
Connect with Cloudtech today to design a security strategy that keeps your data safe while fueling innovation.
FAQs
1. Why is cloud security different from traditional on-premise security?
Cloud environments are dynamic, elastic, and operate on a shared responsibility model. Unlike on-premise systems where IT owns everything end-to-end, in the cloud, AWS secures the infrastructure while SMBs are responsible for securing their workloads, identities, and data. This requires continuous monitoring, automated controls, and zero-trust principles to stay protected.
2. What mistakes do SMBs commonly make when setting up cloud security?
Common pitfalls include granting broad IAM permissions (like full admin access), storing sensitive data without encryption, treating cloud as if it were on-prem (leading to outdated defense models), and skipping automated logging or monitoring. These gaps often go unnoticed until an incident occurs, making proactive best practices critical.
3. How does automation improve SMB cloud security?
Manual processes are error-prone and can’t keep pace with evolving threats. By automating compliance checks, access reviews, vulnerability patching, and anomaly detection, SMBs ensure consistent, real-time enforcement of security rules. Services like AWS Config, GuardDuty, and Security Hub help eliminate human oversight while reducing operational workload.
4. Can SMBs achieve enterprise-grade security without enterprise budgets?
Yes. Cloud-native security is inherently scalable and pay-as-you-go. Tools like AWS WAF, Shield, and CloudTrail give SMBs access to enterprise-grade capabilities at manageable costs. With proper architecture and governance, SMBs can deploy multi-layered defenses affordably, getting protection once reserved for large enterprises.
5. How does Cloudtech ensure security remains effective as SMBs grow?
Cloudtech builds adaptive security frameworks aligned to AWS best practices. That means identity controls, monitoring pipelines, and compliance checks are designed to scale automatically as workloads expand. By combining automation with ongoing advisory support, Cloudtech ensures SMBs maintain a proactive, compliant, and resilient security posture at every stage of growth.

Get started on your cloud modernization journey today!
Let Cloudtech build a modern AWS infrastructure that’s right for your business.